Cybersecurity Home Lab - Configuring Pfsense Firewall
- Jv Cyberguard

- Feb 20, 2023
- 6 min read
Updated: Jul 18, 2023

Lab Introduction
For both aspiring and professional security analysts, having a home lab is important to gaining familiarity with tools, configurations, and attack simulations.
This home lab is inspired by Day Cyberwox's lab but a few modifications were made along the way to demonstrate initiative and create additional functionality.
I built out this lab so that I could gain additional experiencing in configuring SIEMs, firewall administration, system administration, and most importantly have a platform to practice offensive and defensive skills across the home lab environment.
Hardware specs of my PC
Storage: Samsung SSD 970 EVO 1TB M.2
RAM: GSkillz DDR4 32GB
CPU: AMD Ryzen 5 5600G
Motherboard: MSI B550m PRO VDH Wi-FI
Form factor: ATX
Part 1- Configuring pfSense
In this part of the lab, we will install VMware workstation pro as the hypervisor so firstly install VMware Workstation Pro. Next step is to download pfSense. The links for both of these are below.
VMware Workstation Pro:
https://www.vmware.com/ca/products/workstation-pro/workstation-pro-evaluation.html
pfSense firewall:
https://www.pfsense.org/download/
pfSense will configured as the firewall to segment the network and route traffic and will only be accessible from the Kali Machine. When pfSense is downloaded it will have the .gz extension which indicates that it is compressed. So we will use 7-zip to decompress the iso. Once you have VMware open, we can get started by clicking Create a New Virtual Machine.

In the wizard, click Typical > Installer disc image file (browse for the pfSense iso download)> Name the virtual machine pfSense > Store virtual disk as a single file > Customize Hardware. You can find out the minimum hardware requirement on the pfSense website. If your machine has similar specs to mine you can provision pfSense as below on the customize hardware screen. Initially, the VM only had one network adapter but based on the topology, we will need 6 interfaces for this lab. So click add then select network adapter and continue to do this until there are 6 in total. Also, remove things we do not need such as USB controller and sound card. The result of following the instructions in this paragraph should be as in the screenshot below.

Please refer to the topology image at the outset as I explain below how each of these adapters will be used by the pfSense firewall to support network segmentation, security, and connectivity throughout the Homelab environment.
pfSense Interfaces | Description | Virtual Network |
Network adapter (em0) | The connection out of the virtual environment (our WAN) to the host pc then to the internet where we will sync our AD with Azure AD | It will be connected to VMnet8 which is the default NAT network in VMware |
Network adapter 2 (em1) | The connection to the Kali machine which will be our attack machine and management interface | It will be connected to VMnet2 |
Network adapter 3 (em2) | The connection to the Victim Domain network which will simulate a corporate environment | It will be connected to VMnet3 |
Network adapter 4 (em3) | The connection to our all in one IDS Security Onion | It will be connected to VMnet4 |
Network adapter 5 (em4) | A span port that receives all the frames from the interface connected to the Victim network. Security Onion monitoring interface will listening over this adapter | It will be connected to VMnet5 |
Network adapter 6 (em5) | The connection to our Splunk instance which is our SIEM which will be ingesting Windows logs from the domain controller on the Victim Domain network | It will be connected to VMnet6 |
When the machine boots we will be greeted with the pfsense installer window. At this point, we should accept all the defaults. Use this doc as a ref guide on how to install. https://docs.netgate.com/pfsense/en/latest/install/install-walkthrough.html
The only selection in the walkthrough in the documentation that I suggest doing differently is the partitioning part of the install make sure to click Auto (UFS) BIO -Guided Disk Setup using BIOS boot method because that is what worked for me. It will begin installing firewall to the target disk. After installing, it would prompt to open a shell but you will select NO here. Then we will select reboot.
At the next startup we should be met with the screen below where we will press 1 to create the interface mappings.

It will show us the valid interfaces available and then ask the prompt below to which we will say no.

The next prompt will be to enter the interface names for the network adapters. Follow the pattern below.

Continue to respond to the prompts such that the interfaces will be assigned as follows:

We now are going to configure the interface IP addresses by entering 2 at the pfSense menu. It will ask us to enter the number of the interface that we wish to configure and as in the picture below we will begin with LAN (em1) which is numbered 2 on the list of available interfaces. This will also be the Ip we will be using to access the web interface to administer the pfSense firewall later on.

The beginning of the IP address range below should be 192.168.1.10 instead of .11

We will continue assigning in the same pattern of giving each adapter its own /24 subnet. Except for the others we will not be enabling DHCP.
So in conclusion for this part, em0, was the WAN adapter with IP received via DHCP, em1 is the LAN adapter with IP 192.168.1.1, then em2 which is on vmnet3 will be assigned IP 192.168.2.1, em3 which is on vmnet4 will be assigned IP 192.168.3.1, and em5 which is on vmnet6 will be assigned 192.168.4.1 and we will leave em4 which is on vmnet5 for now because as shown in the topology it will be configured as a span port to allow us to monitor traffic using security onion. So essentially the devices that are connected to the firewall have to be assigned IP addresses in the same subnet. The pfSense configuration should look the same as below and feel free to correlate to the topology and the table.

Now, the base installation of pfSense is complete we now need to create a firewall rule to facilitate internet access and installation of other tools behind the firewall.
To further configure pfSense we need to access it through the Web Configurator at the IP listed. However, we need a machine to do this from. According to our Topology this is where we install Kali Linux. While it will be an attack machine, it will also be where we solely access and administer our firewall from.

You can download it at https://www.kali.org/get-kali/#kali-virtual-machines.
You have to unzip it using 7zip.

Since we are downloading a prebuilt VM, once it is extracted all we have to do is click on the .vmx file in the kali-linux vmware folder and it will open in VMware.

Go to settings.

Change the network adapter from NAT to VMnet2. Then power on the VM and allow it to load. Open terminal, run ifconfig command and you should have received an IP from the pfSense.


The login credentials is kali/kali by default. To change it we type passwd in terminal.
Now remember that we want to use this machine to access pfSense web portal so open firefox and type in the IP to access pFsense.

Click advanced >Accept the risk and continue
The default username is admin and the default password is pfsense.
We will now configure the rest of pfsense through the presented wizard.
Add the primary and secondary DNS servers as 8.8.8.8 and 4.4.4.4 respectively.
On the next page, choose your timezone.
Then we go to the next page, 'Configure you WAN Interface' and scroll down to the bottom. We can scroll down to the bottom and untick these options.

We leave the default on the 'Configure LAN interface' page.

On the next page we want to set a new password.

Then click reload, to reload pfSense with new changes.
We will now begin further configuring the interfaces in the web configurator. To do this we will navigate to Interfaces in the top menu and we will start with LAN which would be vmnet 2 for kali on subnet 192.168.1.1
We will change the interface name from LAN to KALI, since it is for the kali machine. Save and apply configuration changes.

We will then configure OPT1 which is interface 2 (em2) by naming it Victim Domain. So essentially each interface will be a different subnet connected to pfsense via all of its network adapters/interfaces.

In accord with the network topology, interface 3 (em3) is on vmnet4 which connects to security onion. Therefore we name it that.

As we go over to opt3 you would realize we do not have an IP address. This is because we did not set interface IP address for it like we did with the others. Therefore, we will have to enable it and name it. This will be our span port and vmnet 5.

The last one we will configure will be splunk. Which is our vmnet on interface 5 (em5). As the name suggests we will be connecting our splunk instance to our network from this interface.

You can verify the assignment by clicking on interfaces then navigating to interface assignments. It should look like this below

We next want to add a bridge by clicking here:

Click ADD. We will now select the victim domain as our member interface for the bridge and the click display advanced go to span port and select SPANPORT as the span port. As the description states, every frame received by the bridge from the victim domain will be copied to the span port and we will then have the frames sent to SecOnion via on interface 4(em4) vmnet 5

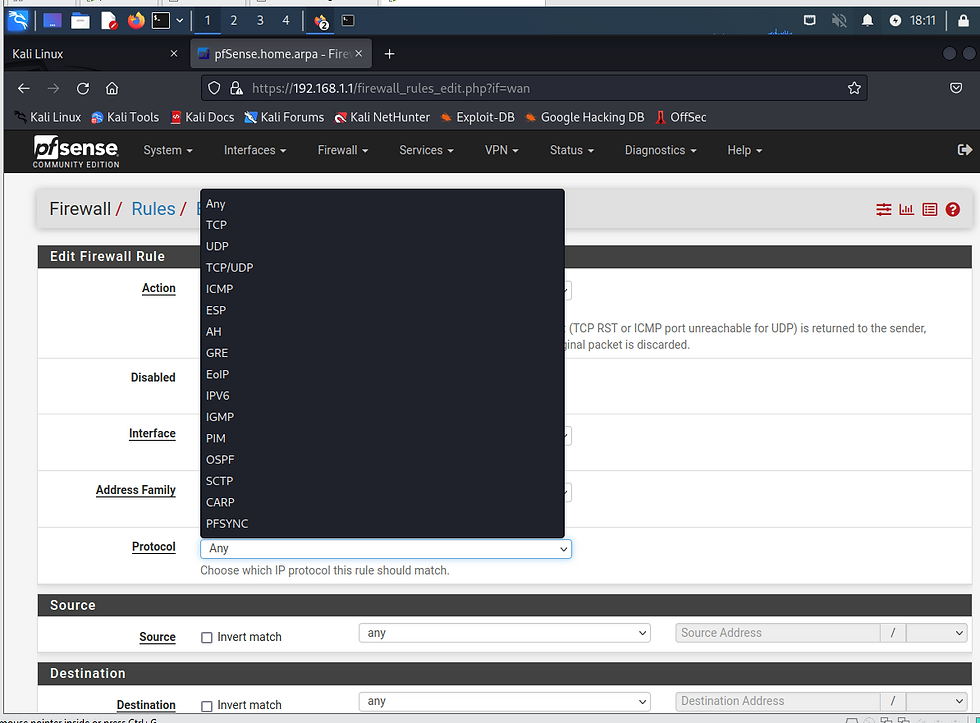
Next we will go to firewall > rules > Under WAN select > add(top of the list) > then edit the protocol to allow any. Make sure the action is set to Pass > Apply changes. The reason why we are opening up the firewall is to make It more vulnerable so that we can see some alerts in action. Take a snapshot of you pfSense Firewall at this point. To do that right c;ick the VM.
We will next click SecOnion and add(top of the list) the same rule.


I would say do this any any for all interfaces you are trying to establish connections for now.
Then we will tighten them to allow based on what services and protocols need access in a firewall hardening lab.



Thanks for this article. Keep it like that and share more content and knowledge for basic home and small business environment.